In the past year, ransomware has continued to evolve and become more pervasive. In fact, version 4.0 of the Crypto variant of ransomware was discovered in early November. This version not only encrypts the file content, but it also scrambles the file name upon infection.
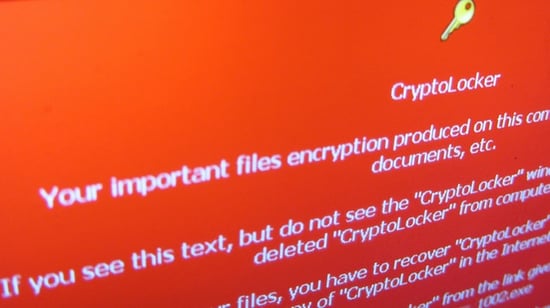
This FBI alert describes how ransomware works, in particular, the Crypto variants.
This virus encrypts files on a computer’s hard drive and any external or shared network drives to which the computer has access. It directs the user to a personalized victim ransom page that contains the initial ransom amount (anywhere from $200 to $5,000), detailed instructions about how to purchase Bitcoins, and typically a countdown clock to notify victims how much time they have before the ransom doubles.
An organization can fall victim to ransomware when an employee opens an infected email attachment, clicks on a link in a malicious email, clicks on or is targeted by an infected advertisement (malvertising), or visits a compromised website. Even law enforcement agencies have had their files locked down by ransomware.
Take a Proactive Approach Against Ransomware
Don’t put your organization in a reactive position where the only solution is to pay ransom to a criminal. Even if you pay, you may not get your files back. Associations can improve their security exponentially by focusing resources on the following:
Don’t get caught without an effective backup system.
If ransomware encrypts your files on a shared network drive, you have two options for decrypting: pay the ransom or restore from backup. The first option isn’t foolproof as you may not receive the decryption keys from the criminals—they are criminals after all. Your best, and only, other option, is to restore the files from backup.
I consider working, functional backups to be the most critical component of any IT system. In fact, I ask this question—what is the most critical component of any IT system?—during interviews and if the candidate says “backups,” they are immediately hired. Ok, not immediately, but it is that important.
Your IT team should test data restores on a regular basis so when it’s time to restore critical data, there won’t be any surprises. Ideally, a restoration test should be done once a week. In practice, it probably won’t happen that often. Our Network Operations Center team does get a lot of practice, because we typically perform one or two restorations per week across our entire client base in order to recover accidently deleted or misplaced files; it just comes with the territory of our NOC experts.
Organizations should also use multiple layers of backups. For instance, Windows Server includes a technology called Shadow Copy that allows for data to be ‘snapshotted’ on a regular basis. These snapshots can be utilized to restore data and are often the fastest option for ransomware recoveries.
Consider security awareness training for staff.
You have to operate with the assumption that someone on staff will eventually access a non-legitimate website, whether intentionally or not, or a compromised legitimate website. This scenario is one of the most likely instances of security weakness for an organization.
One way to prevent this scenario is to require all staff to attend a security awareness training session. However, security awareness training must be treated like any other project—you must have defined and measureable goals. Compensation to the trainer should depend upon successfully meeting these goals. For example, after staff has completed the training, the security awareness trainer should send fake phishing emails to test the staff’s new knowledge. Training will be deemed a success if the click-through rates are below a specified threshold.
If no one on your IT staff is qualified to deliver security awareness training, hire a technology consultant. Provide the training to all new employees as well as ‘booster’ sessions throughout the year for everyone.
Take a multi-layered approach to security.
Firewall and desktop/laptop anti-virus software aren’t sufficient for security. On top of that software, you must also layer firewall intrusion prevention functionality, strong password policies, and web/malware filtering software, such as OpenDNS.
Since we’ve started using OpenDNS for our clients, incidents of malware/virus infections, particularly ransomware infections, have been significantly reduced. OpenDNS protects customers from malware, botnets, phishing, and targeted online attacks by filtering web-related data requests and making sure websites are legitimate. If a legitimate website has been hacked or if its URL has been changed so it redirects to a malware site, OpenDNS will block the user’s access to that link.
Proactively monitor, test, and apply patches to all systems at least once every 6 weeks.
It’s not enough to simply allow the automatic update functions of your operating system to protect you. Third-party applications such as Java and Flash, as well as other third-party browser plug-ins, are inherently insecure. The bad actors regularly exploit these vulnerable applications to inject malware into end-user systems.
Third-party applications must be patched regularly, that is, as often as those patches are released. Don’t get behind, like an automobile recall you keep putting off. One of the advantages of working with a Managed Service Provider (MSP), like DelCor, is that we use tools to push these patches out to thousands of machines in mere minutes.
Make no assumptions about your backup system.
If I were an association CEO, I wouldn’t assume my IT department has a firm, practiced handle on backups. Instead, I suggest gathering your IT team and asking them these questions. If you want to validate your organization’s backup processes and procedures, a technology consultant can help.
- How often are complete backups made?
- Where is the data stored?
- How do you do it? What is the process?
- How often do you perform a test restore?
- How long is backup data retained?
- Do we have multiple layers or systems of backups? For instance, traditional online backups and server shadow copies?
Your IT department or MSP should identify all the servers in your control and document how the data residing on that server is backed up. You don’t want to miss any data. Then, your backup policy should be documented and followed to the letter.
But, that’s not all. What about the data you own that’s on servers not in your control, for example, servers run by your SaaS vendors? What’s the backup policy of your AMS or LMS vendor? How often do they test and restore? Are their recovery time objectives defined in your contract with them?
Here’s a scenario to consider. If you move your email to Office365, what happens if you have a corrupted mailbox or someone accidently deletes a subfolder? How do you get it back?
Here’s the bad news, you can’t always get that subfolder back. Microsoft’s backup methods are half-measures, which is probably fine for 99% of their clients, but may not help you when you really need it. Microsoft’s price advantage comes with that backup disadvantage. However, third-party solutions have been introduced onto the market that will back up 365 data on a daily basis.
Not if, but when.
As shown by the recent security breaches at Target, Sony, and even the CIA Director’s email, a security breach at your organization is not a case of if, but when. Given this new reality, your organization must have solid breach response and data recovery plans in place for a security breach. These response plans should utilize your existing IT practices and procedures, such as backups, to minimize downtime and data loss.
Looking for more information about information security? We’ve got you covered. Complete our cybersecurity assessment, or check out our eBook The Cybersecurity Watchlist for Association and Nonprofit Executives for more information on threats to your organization’s security and how you can prevent your data from being compromised.
Flickr photo by Christaan Colen

