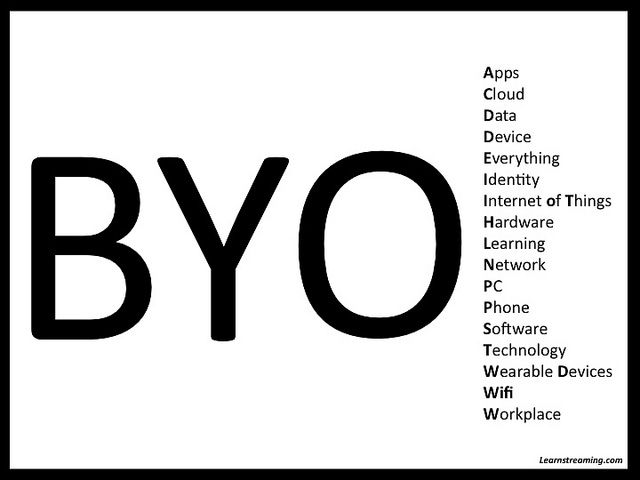
BYOD is here to stay. In the BYOD 1.0 phase, IT departments were focused on managing employees’ mobile devices – a task that caused friction with everyone else on staff. As associations enter the BYOD 2.0 phase, the focus will be on managing applications and being a resource, not a pain, to the rest of the building.
Employee use of smartphones and tablets is increasing. According to the Cornerstone OnDemand report, 52% of Millennials and 23% of older generations use their smartphones for work. 20% of Millennials and 10% of older generations use their tablets at work.
The BYOD trend is turning into the “bring your own service” (BYOS) mentality. Instead of only using applications approved by the IT department, employees are using public cloud services, such as Dropbox and BaseCamp, to do their work. The extent of this loss of control – a source of stress to IT directors – can also be seen in organizational budgets. At 100 of the “top performing” companies participating in the PricewaterhouseCoopers’ Digital IQ Survey, the IT department now controls less than 50% of technology expenditures.
The benefits and risks of BYOD and BYOS
IT departments are finding ways to sanction the cloud-based storage and file-sharing apps that employees prefer to use. The BYOS approach has benefits…
- Freedom of choice and flexibility – Staff uses the most efficient, familiar, and user-friendly tools for the job.
- Convenience – Employees want to work without being tethered to their work desktops, or even laptops.
- Collaboration – Staff and members have more online options for working together.
- Productivity – Schedule and location don’t hinder staff’s ability to get work done.
…but it also has drawbacks. Employee use of unsanctioned IT resources outside the supervision of the IT department – “shadow IT” – is a risky business.
- Confidential member and financial data must be protected in secure locations.
- Organizations that handle certain types of information, such as credit card data, must meet compliance and audit standards.
- The IT department must not encroach on employee privacy while managing their devices.
- When an employee leaves the association, you must know where data is stored and have access to retrieve or erase it.
Reducing the risks of BYOD and BYOS
Many organizations require the use of mobile device management (MDM) software for all employee mobile devices that connect to the employer’s systems. MDM allows IT departments to provide services on cloud and network platforms while providing control of organizational data. It gives IT staff the ability to remotely secure and/or wipe organizational data from a mobile device when it’s lost or stolen or when an employee leaves the organization. Most MDM systems also allow you to separate business and personal apps.
Mobile phone vendors are starting to provide enterprise solutions that allow organizations to maintain the control they need while protecting employee privacy. Some new phones run two operating systems to keep personal and business information completely separate and come with data encryption, synchronization, and MDM.
Approaches to BYOD management
When IT directors don’t have to battle to retain control of devices, they can instead focus on managing risk and helping employees find the best tools and services to use for their work. BYOD policies and procedures that are easily understood and regularly communicated will help, rather than hinder, employees. These policies should:
- Require that departments and employees notify and/or consult with the IT department about the devices and/or cloud services they use for work.
- Identify who gets association phones (if anyone), who gets reimbursements (and for how much), and who’s responsible for purchasing, repairing, and/or replacing phones.
- Clarify which devices are supported and who provides support.
- Mandate staff training to mitigate data/privacy risks.
- Require that the IT department is notified within a specific period of time when a mobile device used for work is stolen or lost.
- Identify who gets network access, when, and how much.
- Include vacation and termination procedures.
The IT department has the opportunity to lead associations during this transition from command-and-control IT to collaborative IT. By understanding the needs of employees, the IT department helps staff manage their mobile devices and select appropriate cloud services. As the line continues to blur between personal and professional lives, devices, and applications, an agile IT department becomes a business partner with other departments, providing technical support and knowledge that empowers association staff to do their best work.
The ASAE Technology Conference in Washington, DC, is December 3-5, 2013. Bring your device to #tech13 booth 501 for a chance to talk with us about MDM – and lots of other acronyms.
BYO Flickr photo by DennisCallahan; Chief & Chuck Flickr photo by cainc
