When your IT department announces a new security procedure, is “Argh!” the first thought crossing your mind? I’ll admit it: I grumbled to myself when our IT team told us we had to use two-factor authentication when logging in to some of our systems.
I shouldn’t have been surprised. Around here, the cybersecurity battle cry has always focused on protecting the crown jewels—any system or tool containing important data, whether ours or our clients’. So much is at stake that we use every possible weapon in defense of that data.
Implementing—and loving—2FA at your association or nonprofit
How two-factor authentication works
When the IT team added two-factor authentication (2FA) to our remote access and time tracking systems, I thought it was a huge pain in the tukhus. In reality, it takes less than 10 seconds extra to log in with 2FA—no big deal.
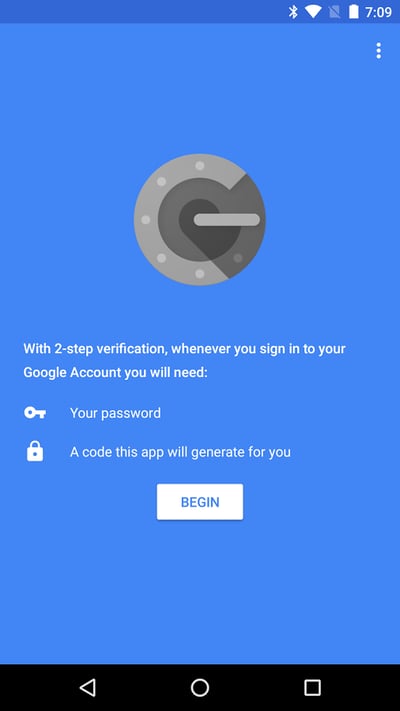
After entering my credentials, I receive a randomly generated 6-digit code on the Google Authenticator app on my phone. This code times out every 30 seconds—providing the opportunity for geeky entertainment (more on that later).
We also use a soft token authenticator that offers another layer of defense. In addition to your normal password, you enter a PIN you choose as well as a randomly generated 8-digit number.
Making two-factor authentication work in your personal life
As I became more accustomed to 2FA and reflected on the dangers of not having its protection, I added it to my personal Google and Apple accounts. Think about it: if hackers get access to your email inbox, they can change your password on other accounts—unless you have 2FA set up on those accounts.
My 2FA enlightenment returned when my iPhone recently took an unexpected bath. After a trip to the wireless store, I now have a new iPhone 7 that’s supposedly waterproof. To make sure I could access DelCor systems on my new phone, our tech support team loaded and configured everything the right way.
This episode demonstrates my dependence on hand-held devices for doing business, and probably yours too. But, we must also be cognizant of the importance of our phones to our organizations. Unless you keep them safe and locked down, phones can provide hackers access to your systems and data. Please check the security settings on your mobile devices and make sure you’re in compliance with your organization’s BYOD policy.
Introducing two-factor authentication to your colleagues
So much is riding on the security of your association’s data and technology that you simply must require 2FA on any systems with sensitive data. But, don’t add 2FA to everything just for the heck of it.
When the IT department goes to extremes to protect everything, you end up creating security gaps because staff will find ways to work around nonsensical security measures. Find the sweet spot for your association’s IT security: secure only what needs to be secured, and know the difference.
Anticipate grumbling when you introduce 2FA—after all, few people truly enjoy change. Demystify 2FA for them. Make the business case about what needs protecting and why. Demonstrate how 2FA works and why it’s worth the extra effort, however small. Remind them: they don’t want to be the weak link.
Recently I realized how far I’ve come from 2FA curmudgeon to 2FA advocate—you might even say 2FA geek. Now, before I start logging in, I reach for my phone because in a strange game I’m playing against the Google Authenticator, I want to beat its timeout. Don’t judge.
Two-factor authentication started out for me as a major pain. Then it became a minor inconvenience. Now, I think of it as part of doing business. When your IT department introduces 2FA, and they better, give them a break and accept it without grumbling.
Familiarize yourself with other security risks that may lie in the hands of your staff, or elsewhere in your organization. Download our free infographic, Is Your Association Protected from Cyberattacks?